Key Management System
Keys are the one of most important and integral assets of any organization. Most of the organization maintains physical log book for keys taken and return time by the authorized persons for various rooms/ locks/ lockers/ safe rooms/ hazardous areas. Such traditional key management is inefficient, unreliable and makes tracing of keys a difficult task. If keys of such important areas get into the wrong hands then it becomes very difficult task to change the locks of each door. Also, it is a security breach and against safety standards.
To avoid all the above mentioned limitations and threats, controlled Electronic key management system shall be required which shall be more accountable and easy to maintain.
Working principle
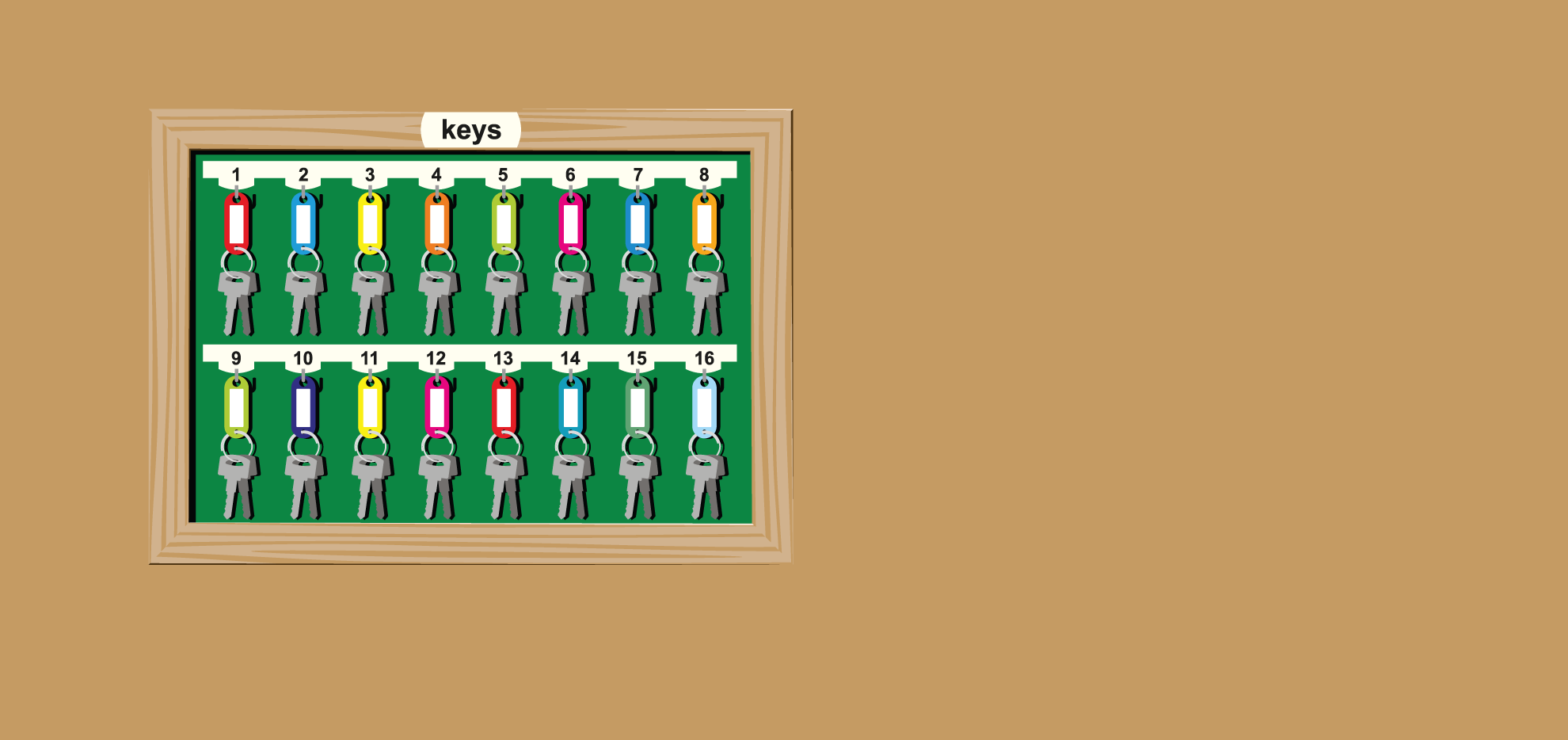
Electronic key management system is scalable modular system comprises of wall/ floor mount cabinet (cabinet size varies on the no. of keys placed inside cabinet). Door of the cabinet is access controlled.
Access control security levels can be as per security requirement (for e.g. door can be open after showing authorised access card (Radio Frequency Identification) to the card reader which is integrated part of the cabinet or with authorised access card and pin code (this pin code can be given to the authorised personnel or it can be one time pass code received on his/her cell phone).
Inside the cabinet no. of keys are placed in key slots which are provided with locks. These keys can be smart keys or normal keys tied to keychain or key fobs. Only authorised person can have access to the key/keys which is/are assigned to him/her. Rest of the keys shall remain in locked position. After use of the key, the same shall be put in the key slot to lock the key in key slot.
KMS software plays an important role for managing KMS effectively. The software can provide following features
(a) Configure users rights for the keys with RFID cards
(b) Tagging of the key slots are not required so any key can be put in any free slot
(c) Lock and unlock of key with light/ LED indications
(d) Simple transaction reports
(e) Alarm indication against the tampering to the panel
(f) Alarm indication against the lapse of predefined key out time
(g) Web based application software to monitor the system remotely
(h) Inbuilt speaker with pre-recorded messages to guide the user
(i) Limitation on per day usage of key
Application
(a) Hospitals (b) Banks
(c) Government and corporate office (d) Malls
(e) Fleet management (f) Shops
(g) Petrol pump stations (h) Safe management.
Advantages
(a) Easy to assign users
(b) User and usage logs can be maintain easily
(c) Safe and secure operation
(d) Easy to manage large no. of keys requirement
(e) Remote monitoring of key usage is possible







